HIPAA Security Incident Report
Enregistrer, Remplir les champs vides, Imprimer, Terminer!
How to create a Hipaa Security Incident Report? Download this Hipaa Security Incident Report if you are working on IEC, NIST, ISO27001:2013 or other IT and Cybe
Prix: USD 2.99
Téléchargez-le maintenant

Formats de fichiers premium disponibles:
.docx- Ce document a été certifié par un professionnel
- 100% personnalisable
Business Entreprise report rapport Compliance Conformité IT TI information technology informatique Security Sécurité Incident IT SOP Hipaa Incident Report Sample Exemple de rapport d'incident Incident Report Samples Exemples de rapports d'incident GDPR RGPD Concern Préoccupation Iso Phi GDPR template modèle GDPR ccpa iso27001 isms ccpa template nist standard iso it standard iso27001:2013 information security standards pdf security standards definition network security standards cyber security standards uk cybersecurity cyber security compliance standards nist security standards information security standards it security management information security best practices information security policy standards it security security techniques information security management systems cybersecurity standards IT compliance TI Conformité it standard operating procedure it security compliance how long does it take to implement iso27001 iso27001 questions iso 27001 controls list iso 27002 checklist
How to create a HIPAA Security Incident Report? Download this HIPAA Security Incident Report if you are working on IEC, NIST, ISO27001:2013, or other IT and Cyber Security Standards and control objectives.
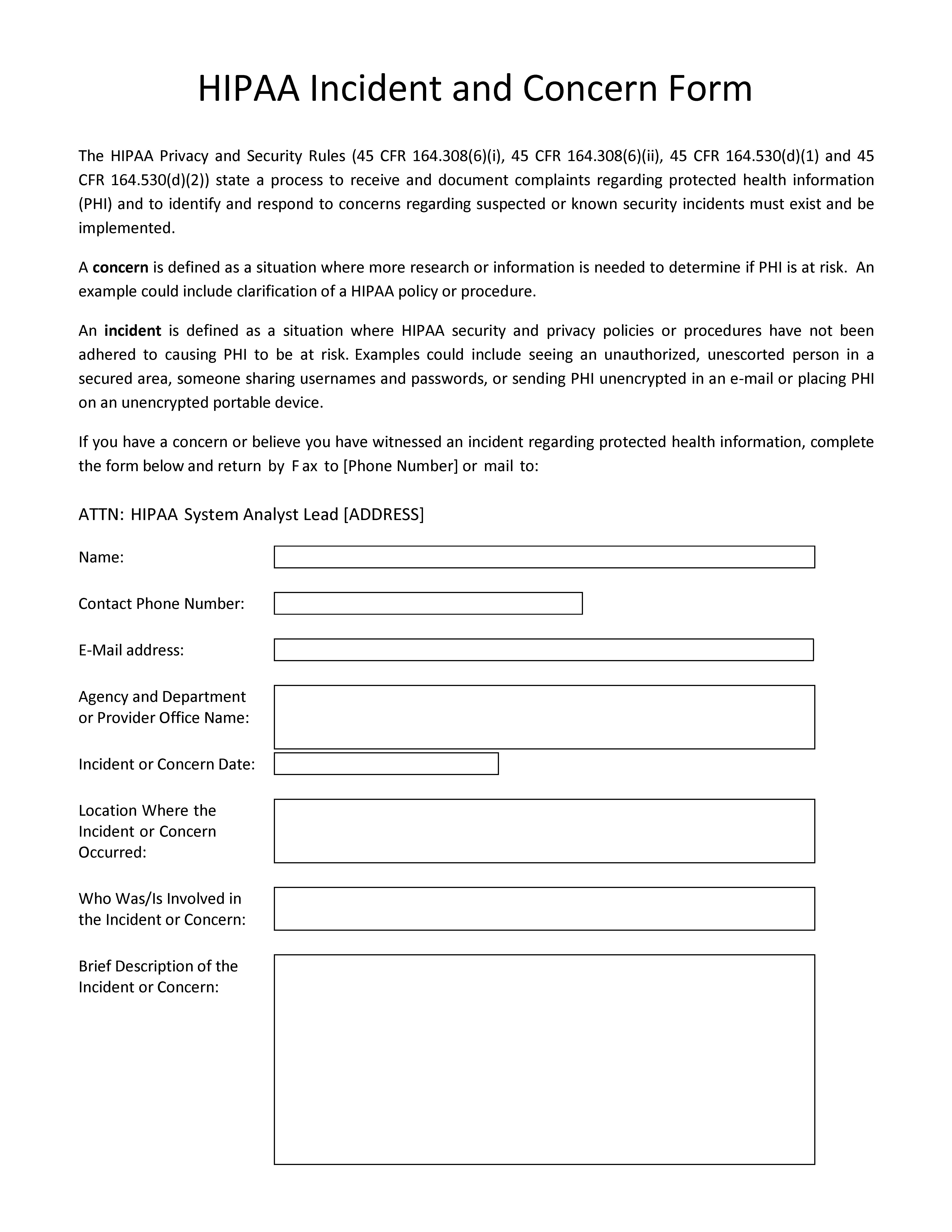
HIPAA Incident and Concern Form The HIPAA Privacy and Security Rules (45 CFR 164.308(6)(i), 45 CFR 164.308(6)(ii), 45 CFR 164.530(d)(1) and 45 CFR 164.530(d)(2)) state a process to receive and document complaints regarding protected health information (PHI) and to identify and respond to concerns regarding suspected or known security incidents must exist and be implemented..
Appropriate data security controls reduce the likelihood (and impact) of data breach incidents during various phases of the data lifecycle. The purpose of this standard is to set out the rules for securing the companies' data during transmission and storage. This document provides best practice recommendations on information security management for use by those responsible for initiating, implementing, or maintaining information security management systems (ISMS).
Nowadays, with the digitalization of our society, the need for data protection became more important. The latest IT Security Standards involve the application of technology to broader social and institutional contexts, and thereby contributes to the servitization of companies, and affects how they compete and interact. This document contains security technology solutions to protect data classified as “Highly Sensitive”, “Sensitive”, “Private” or “Public” as per the Data Classification Standard and Data Handling Guidelines. Specifically:
- Cryptography – Encryption and hashing solutions for protecting sensitive data when in transit or storage, and
- Data Masking – Data masking is a technology for obscuring sensitive information in non-production environments. Through data masking [Company Name] protects the content of sensitive data in non-production environments to ensure that:
- Application developers, testers, privileged users, and outsourcing vendors do not have unauthorized access to such information.
- The data maintains the referential integrity of the original production data.
Download this HIPAA Security Incident Report now. Besides this document, make sure to have a look at the IT Security Roadmap for proper implementation and this fit-for-purpose IT Security Kit here with over 40 useful templates. The document(s) are easy to modify and can be downloaded directly after purchase.
AVERTISSEMENT
Rien sur ce site ne doit être considéré comme un avis juridique et aucune relation avocat-client n'est établie.
Si vous avez des questions ou des commentaires, n'hésitez pas à les poster ci-dessous.


