Cyber ??Security Incident Dossier
Opslaan, invullen, afdrukken, klaar!
De beste manier om een Cyber ??Security Incident Dossier te maken? Check direct dit professionele Cyber ??Security Incident Dossier template!
Beschikbare bestandsformaten:
.pdf- Gevalideerd door een professional
- 100% aanpasbaar
- Taal: English
- Digitale download (383.34 kB)
- Na betaling ontvangt u direct de download link
- We raden aan dit bestand op uw computer te downloaden.
Zakelijk rapport informatie Technologie Naam Veiligheid Voorbeeld van incidentenrapport Incidentrapport voorbeelden Informatiebeveiligingsincidentrapport Cyber Security Incident Report Cyber Security Incident Report Voorbeeld Cyber Security Incident Report Sample Proces verbaal Informatiebeveiliging
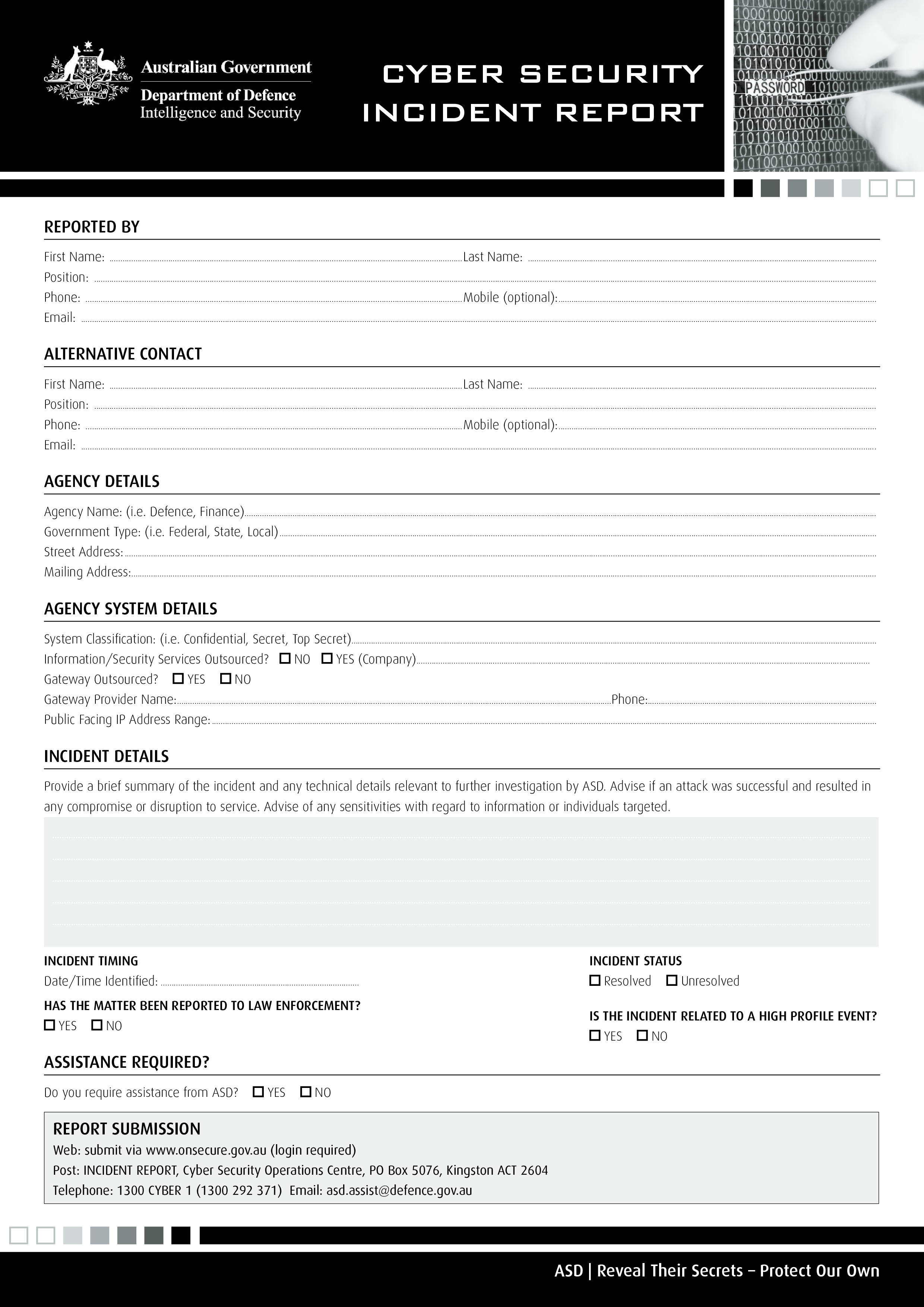
How to draft a Cyber Security Incident Report? What is the proper way to report a potential information security incident? An easy way to start completing your document is to download this Cyber Security Incident Report template now!
We provide this Security Incident Report template to help professionalize the way you are working. Our business and legal templates are regularly screened and used by professionals. If time or quality is of the essence, this ready-made template can help you to save time and to focus on the topics that really matter!
Nowadays, with the digitalization of our society, the need for data protection became more important. The latest IT Security Standards involve the application of technology to broader social and institutional contexts, and thereby contributes to the servitization of companies, and affects how they compete and interact. This document contains security technology solutions to protect data classified as “Highly Sensitive”, “Sensitive”, “Private” or “Public” as per the Data Classification Standard and Data Handling Guidelines. Specifically:
- Cryptography – Encryption and hashing solutions for protecting sensitive data when in transit or storage, and
- Data Masking – Data masking is a technology for obscuring sensitive information in non-production environments. Through data masking [Company Name] protects the content of sensitive data in non-production environments to ensure that:
- Application developers, testers, privileged users and outsourcing vendors do not have unauthorized access to such information.
- The data maintains the referential integrity of the original production data.
I'ts not a matter if the breach has yet been reported to law enforcement or if the case is Resolved Unresolved is the incident related to a high profile event. In any case, assistance is required. Do you require assistance from ASD YeS No report submission Web: submit via (login required) Post: INCIDENT REPORT, Cyber Security Operations.
This standardized Cyber Security Incident Report template with text and formatting as a starting point to help professionalize the way you are working. Our private, business, and legal document templates are regularly screened by professionals. If time or quality is of the essence, this ready-made template can help you to save time and to focus on the topics that really matter!
Download this Cyber Security Incident Report template now for your own benefit! Besides this document, make sure to have a look at the IT Security Roadmap for proper implementation and this fit-for-purpose IT Security Kit here with over 40 useful templates. The document(s) are easy to modify and can be downloaded directly after purchase.
DISCLAIMER
Hoewel all content met de grootste zorg is gecreërd, kan niets op deze pagina direct worden aangenomen als juridisch advies, noch is er een advocaat-client relatie van toepassing.
Laat een antwoord achter. Als u nog vragen of opmerkingen hebt, kunt u deze hieronder plaatsen.