IT Security Analyst Resume
Sponsored Link免费模板 保存,填空,打印,三步搞定!
Download IT Security Analyst Resume
微软的词 (.docx)免费文件转换
- 本文档已通过专业认证
- 100%可定制
- 这是一个数字下载 (11.02 kB)
- 语: English
Sponsored Link
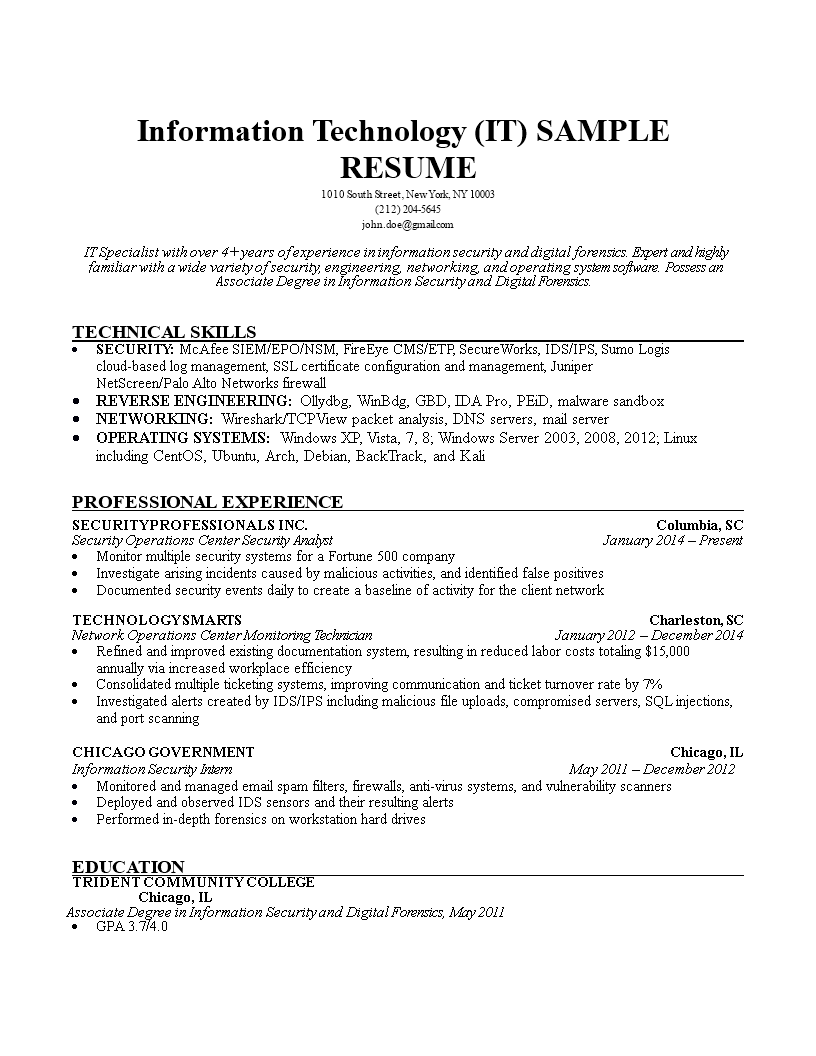
How to grab your futures employers’ attention when you are applying for a new job as an IT Security Analyst? How to draft an IT Security Analyst Resume that will impress? Download this IT Security Analyst Resume template now!
There are a few basic requirements for a Resume:
This Resume template will grab your future employer its attention. After downloading and filling in the blanks, you can customize every detail and appearance of your resume and finish.
You just have to be a little more creative and follow the local business conventions. Also bright up your past jobs and duties performed. Often they are looking for someone who wants to learn and who has transferable skills like:
- IT skills;
- Leadership skills;
- Can do-will do mentality;
- Ability to communicate;
- Ability to multi-task;
- Hard work ethics;
- Creativity;
- Problem-solving ability.
- brief, preferably one page in length;
- clean, error-free, and easy to read;
- structured and written to highlight your strengths;
- immediately clear about your name and the position you are seeking.
Completing your IT Security Analyst Resume has never been easier, and will be finished within in minutes... Download it now!
Security Analyst January 2014 Present Monitor multiple security systems for a Fortune 500 company Investigate arising incidents caused by malicious activities, and identified false positives Documented security events daily to create a baseline of activity for the client network TECHNOLOGY SMARTS Operations Center Monitoring Technician Refined and improved existing documentation system, resulting in reduced labor costs totaling 15,000 annually via increased workplace efficiency Consolidated multiple ticketing systems, improving communication and ticket turnover rate by 7 Investigated alerts created by IDS/IPS including malicious file uploads, compromised servers, SQL injections, and port scanning Information Security Intern Monitored and managed email spam filters, firewalls, anti-virus systems, and vulnerability scanners Deployed and observed IDS sensors and their resulting alerts Performed in-depth forensics on workstation hard drives EDUCATION TRIDENT COMMUNITY COLLEGE Chicago, IL Associate Degree in Information Security and Digital Forensics
DISCLAIMER
Nothing on this site shall be considered legal advice and no attorney-client relationship is established.
发表评论。 如果您有任何问题或意见,请随时在下面发布
Sponsored Link