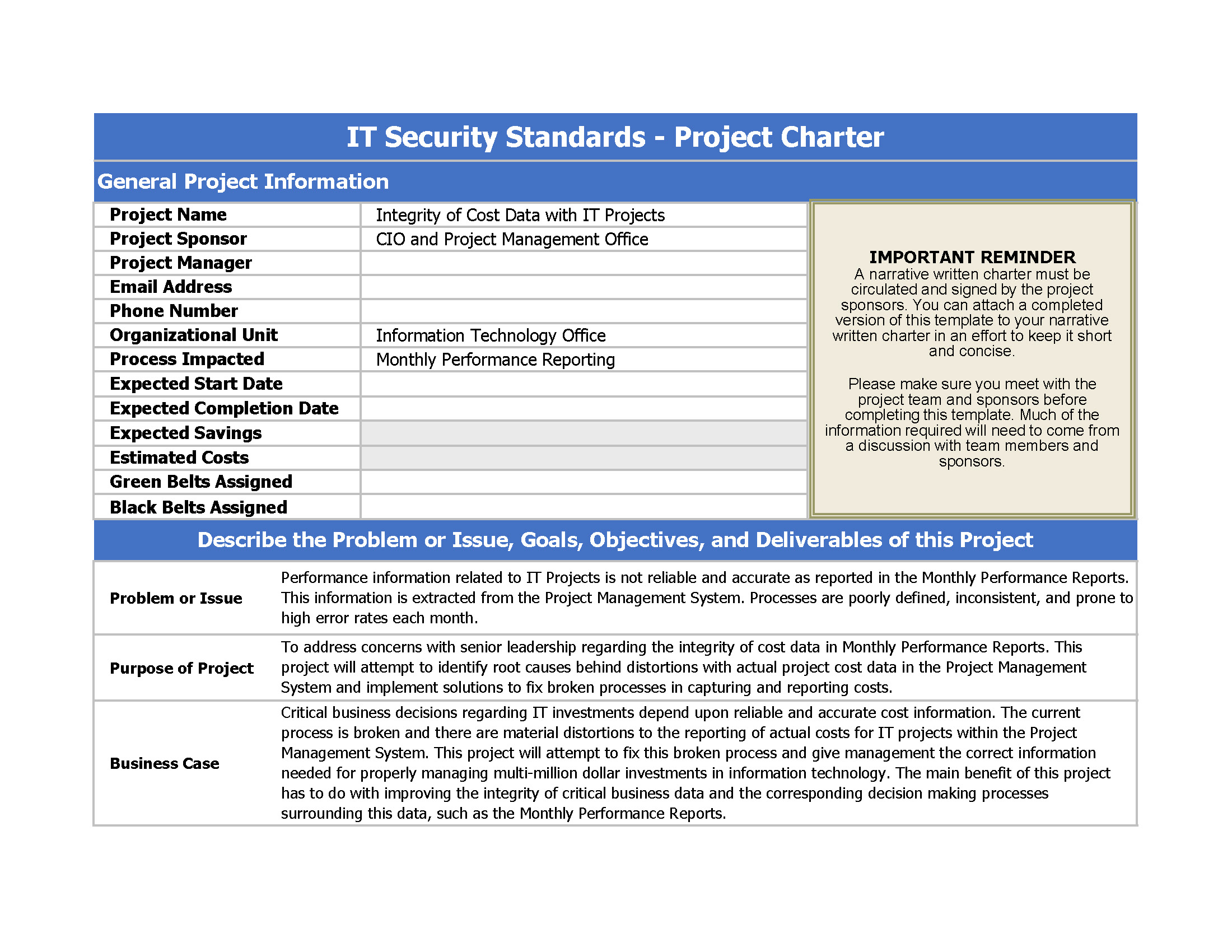
IT Security Compliance Project Charter
Opslaan, invullen, afdrukken, klaar!
How to write a Project Charter for an IT Security Standards implementation project? Check below for the details and download the Project Charter IT Security Standards implementation template

Beschikbare bestandsformaten:
.xlsx- Gevalideerd door een professional
- 100% aanpasbaar
- Taal: English
- Digitale download (29.15 kB)
- Na betaling ontvangt u direct de download link
- We raden aan dit bestand op uw computer te downloaden.
Project management mager zes sigma informatie Technologie
- Project Selection Process;
- Project Description;
- Project Schedule;
- Process Description;
- Project Objectives;
- Project Riscs, Constraints, Assumptions;
- Project Specification Checklist;
- Attachment: Fishbone
- Etc
- Cryptography – Encryption and hashing solutions for protecting sensitive data when in transit or storage, and
- Data Masking – Data masking is a technology for obscuring sensitive information in non-production environments. Through data masking [Company Name] protects the content of sensitive data in non-production environments to ensure that:
- Application developers, testers, privileged users and outsourcing vendors do not have unauthorized access to such information.
- The data maintains the referential integrity of the original production data.
Feel free to download our basic or advanced template designs, they are intuitive and in several kinds of formats, such as PDF, WORD, XLS, etc. Using this project charter template guarantees that you will save time, cost and efforts and enables you to reach the next level of success in your project, work and business!
Download this professional IT Security Project Charter according to Six Sigma project management principles now!
Besides this Excel spreadsheet, make sure to have a look at the IT Security Roadmap for proper implementation and this fit-for-purpose IT Security Kit here with over 40 useful templates. The document(s) are easy to modify and can be downloaded directly after purchase.
DISCLAIMER
Hoewel all content met de grootste zorg is gecreërd, kan niets op deze pagina direct worden aangenomen als juridisch advies, noch is er een advocaat-client relatie van toepassing.
Laat een antwoord achter. Als u nog vragen of opmerkingen hebt, kunt u deze hieronder plaatsen.