Change Management IT Cybersecurity Standard
I-Save, punan ang mga blanko, i-printa, Tapos na!
How to create a Change Management CyberSecurity standard for your organization? Download this IT Security Standard now Standards and control objectives
Ngayon: USD 7.99
I-download ngayon!

Mga magagamit na premium na format ng file:
.docx- Itong dokumento ay sertipikado ng isang Propesyonal
- 100% pwedeng i-customize
Compliance IT information technology IT SOP GDPR Iso Change Management GDPR template Template ng GDPR ccpa iso27001 isms ccpa template nist standard iso it standard iso27001:2013 information security standards pdf security standards definition network security standards cyber security standards uk cybersecurity cyber security compliance standards nist security standards information security standards it security management information security best practices information security policy standards it security security techniques information security management systems cybersecurity standards IT compliance it standard operating procedure it security compliance how long does it take to implement iso27001 iso27001 questions iso 27001 controls list iso 27002 checklist
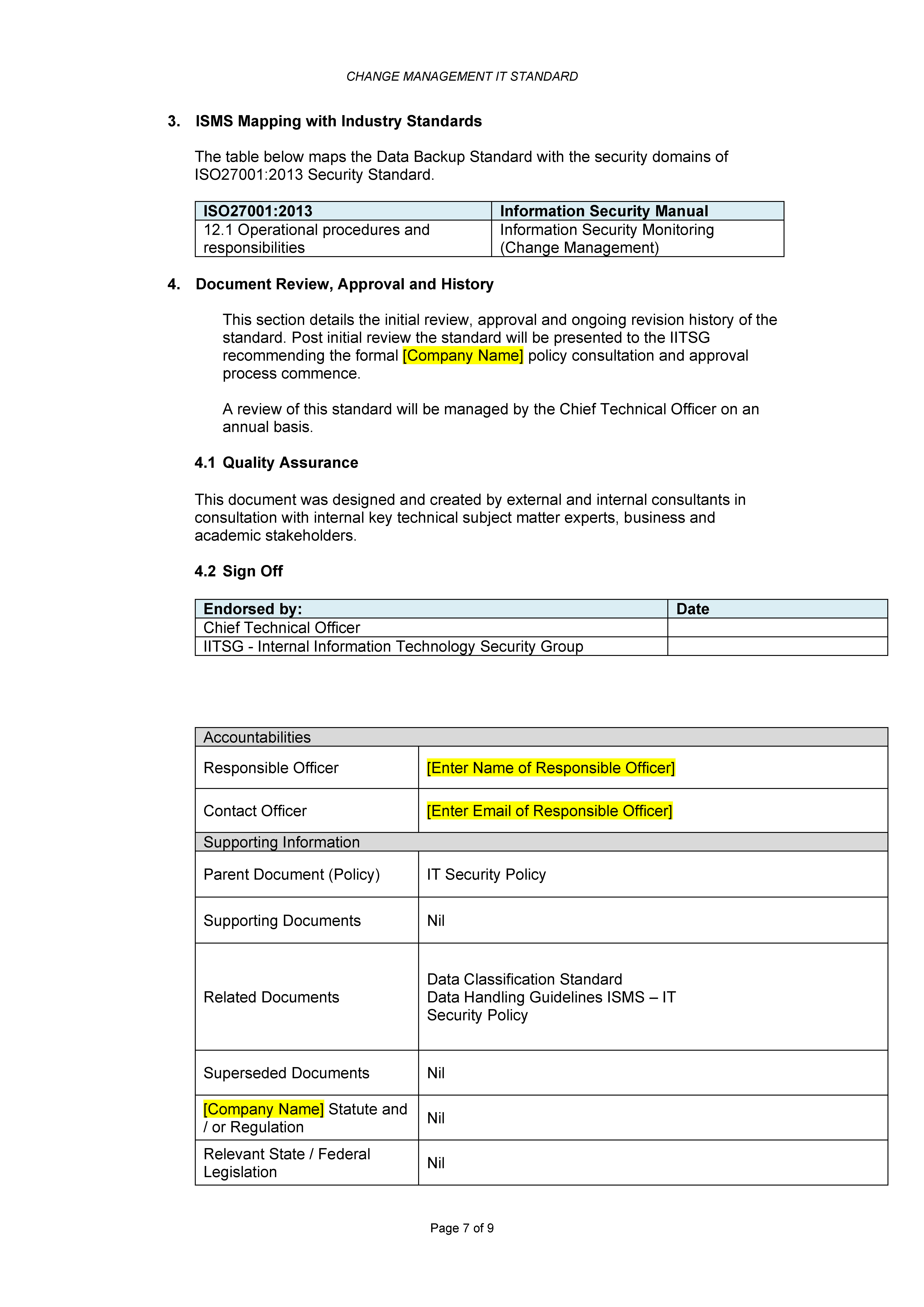
How to create a Change Management CyberSecurity standard for your organization? Download this IT Security Standard for Change Management if you are working on IEC, NIST, ISO27001:2013, or other IT and CyberSecurity Standards and control objectives.
Change Management is an essential IT Service Management discipline, which ensures that changes to services and configuration items are documented, approved, and implemented in a planned and controlled manner. Change Management enables beneficial changes while minimizing disruption to IT Services.
The company utilizes the IT Service Management framework aligned to ITIL, to provide a process-driven approach to the management and delivery of IT Services. Any change to Company production information systems including changes to hardware (servers, storage, network components etc.) and software (operating system, database, application code, configurations etc.) may introduce security risks to the Company's environment. The purpose of this Standard is to ensure that Requests for Changes (RFCs), handled through the Company's Change Management Process are assessed for potential information security risks.
Appropriate data security controls reduce the likelihood (and impact) of data breach incidents during various phases of the data lifecycle. The purpose of this standard is to set out the rules for securing the companies' data during transmission and storage. This document provides best practice recommendations on information security management for use by those responsible for initiating, implementing or maintaining information security management systems (ISMS).
Nowadays, with the digitalization of our society, the need for data protection became more important. The latest IT Security Standards involve the application of technology to broader social and institutional contexts, and thereby contributes to the servitization of companies, and affects how they compete and interact. This document contains security technology solutions to protect data classified as “Highly Sensitive”, “Sensitive”, “Private” or “Public” as per the Data Classification Standard and Data Handling Guidelines. Specifically:
- Cryptography – Encryption and hashing solutions for protecting sensitive data when in transit or storage, and
- Data Masking – Data masking is a technology for obscuring sensitive information in non-production environments. Through data masking [Company Name] protects the content of sensitive data in non-production environments to ensure that:
- Application developers, testers, privileged users and outsourcing vendors do not have unauthorized access to such information.
- The data maintains the referential integrity of the original production data.
Download this Change Management IT Cybersecurity Standard now. Besides this document, make sure to have a look at the IT Security Roadmap for proper implementation and this fit-for-purpose IT Security Kit here with over 40 useful templates. The document(s) are easy to modify and can be downloaded directly after purchase.
DISCLAIMER
Wala sa 'site' na ito ang dapat ituring na legal na payo at walang abogado-kliyenteng relasyon na itinatag.
Mag-iwan ng tugon. Kung mayroon kang anumang mga katanungan o mga komento, maaari mong ilagay ang mga ito sa ibaba.