IT Specialist CV
I-Save, punan ang mga blanko, i-printa, Tapos na!
How to create the perfect CV for an IT specialist? Download this IT Specialist CV template now!
Mga magagamit na premium na format ng file:
.doc- Itong dokumento ay sertipikado ng isang Propesyonal
- 100% pwedeng i-customize
Business Negosyo Resume Information Security Systems Forensics information technology resume Digital Information Technology Resumes
How to grab your futures employers’ attention when you are applying for a new job as an IT Specialist? How to draft a that will impress it's readers! Download this IT Specialist CV template now!
This CV template will grab your future employer its attention. After downloading and filling in the blanks, you can customize every detail and appearance of your resume and finish.
You just have to be a little more creative and follow the local business conventions. Also bright up your past jobs and duties performed. Often they are looking for someone who wants to learn and who has transferable skills like:
- Leadership skills;
- Can do-will do mentality;
- Ability to communicate;
- Ability to multi-task;
- Hard work ethics;
- Creativity;
- Problem-solving ability.
There are a few basic requirements for a IT Specialist CV. Every CV should contain the following:
- brief, preferably one page in length;
- clean, error-free, and easy to read;
- structured and written to highlight your strengths;
- immediately clear about your name and the position you are seeking.
Completing your CV has never been easier, and will be finished within in minutes... Download it now!
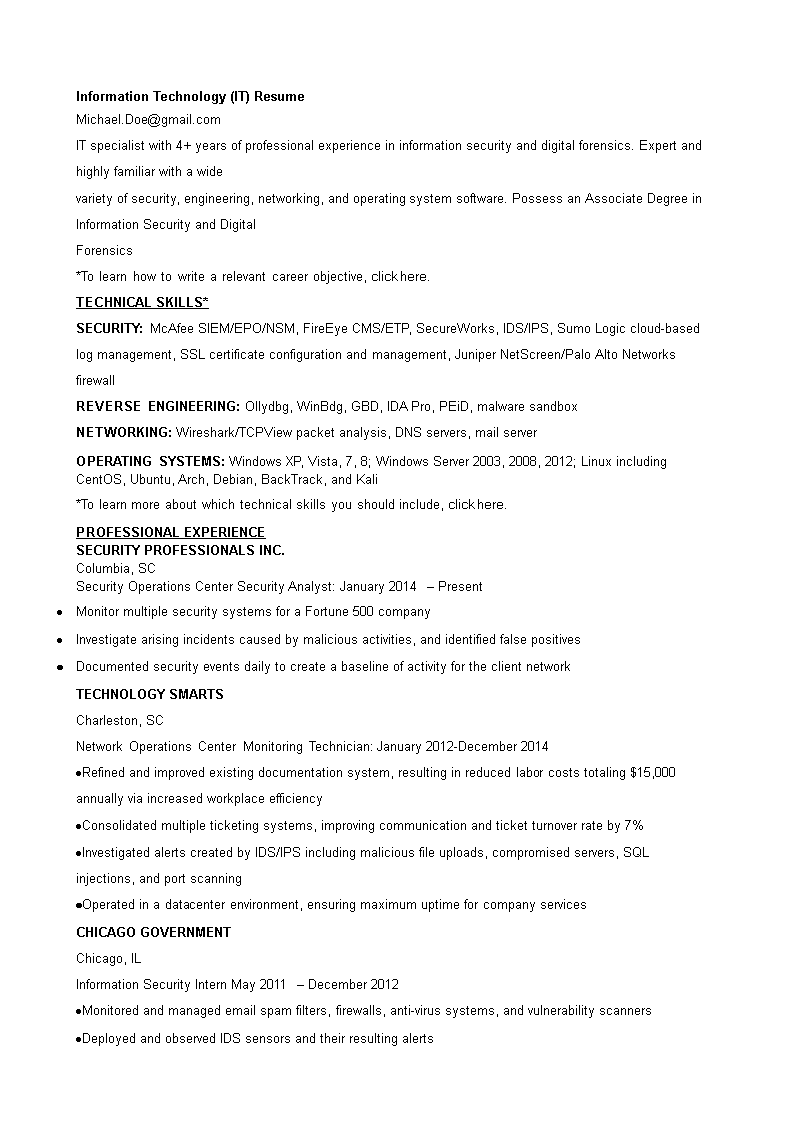
Security Operations Center Security Analyst: Present Monitor multiple security systems for a Fortune 500 company Investigate arising incidents caused by malicious activities, and identified false positives Documented security events daily to create a baseline of activity for the client network TECHNOLOGY SMARTS Charleston, SC Network Operations Center Monitoring Technician Refined and improved existing documentation system, resulting in reduced labor costs totaling 15,000 annually via increased workplace efficiency Consolidated multiple ticketing systems, improving communication and ticket turnover rate by 7 Investigated alerts created by IDS/IPS including malicious file uploads, compromised servers, SQL injections, and port scanning Operated in a datacenter environment, ensuring maximum uptime for company services CHICAGO GOVERNMENT Chicago, IL Information Security Intern Monitored and managed email spam filters, firewalls, anti-virus systems, and vulnerability scanners Deployed and observed IDS sensors and their resulting alerts Performed in-depth forensics on workstation hard drives Investigated various security incidents, mostly the result of malware infections To learn how to quantify your bullet points, click here..
DISCLAIMER
Wala sa 'site' na ito ang dapat ituring na legal na payo at walang abogado-kliyenteng relasyon na itinatag.
Mag-iwan ng tugon. Kung mayroon kang anumang mga katanungan o mga komento, maaari mong ilagay ang mga ito sa ibaba.