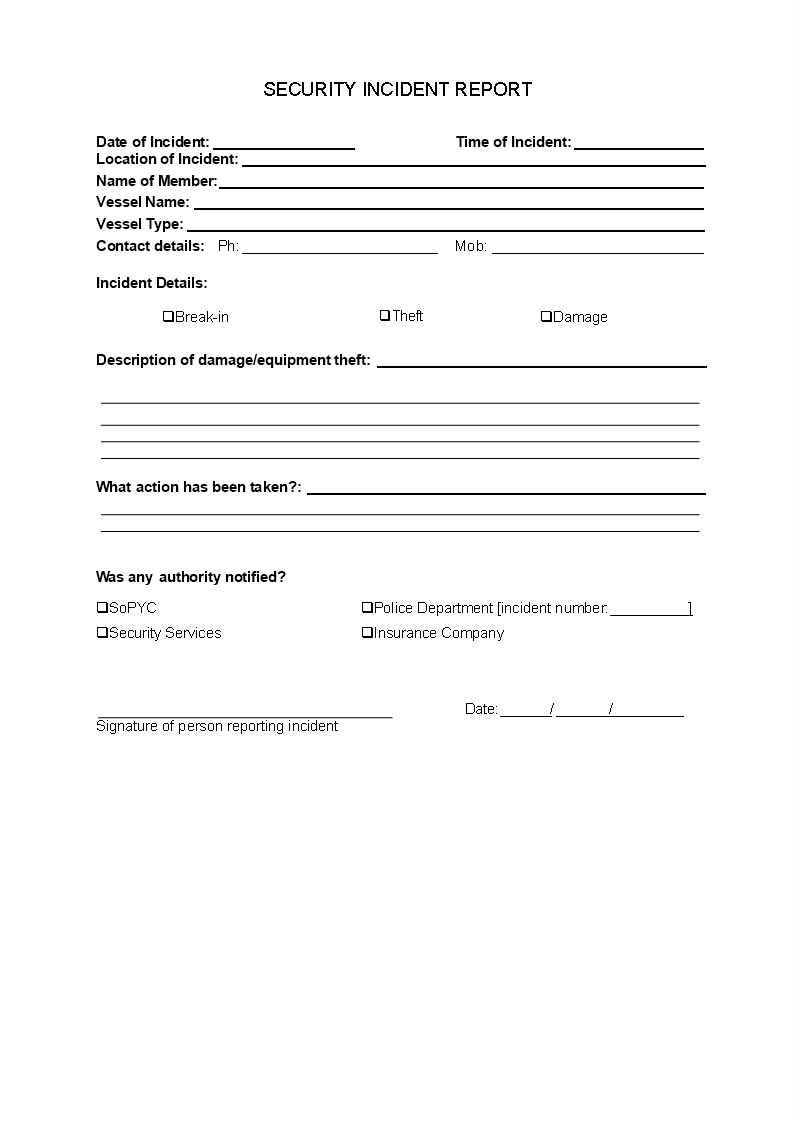
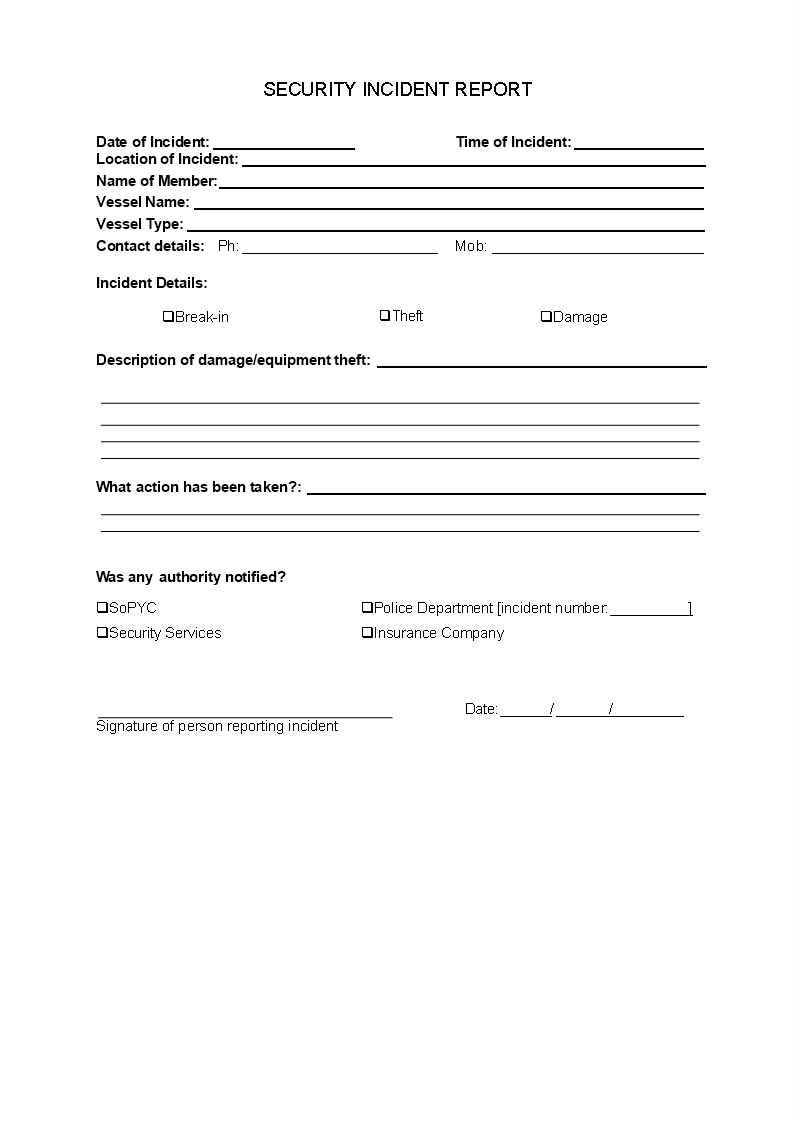
Security Incident Report
Sponsored Link免费模板 保存,填空,打印,三步搞定!
Download Security Incident Report
微软的词 (.docx)免费文件转换
- 本文档已通过专业认证
- 100%可定制
- 这是一个数字下载 (14.78 kB)
- 语: English
Sponsored Link
Are you looking for a professional Security Incident Report? If you've been feeling stuck or lack motivation, download this template now!
This Security Incident Report covers the most important topics that you are looking for and will help you to structure and communicate in a professional manner with those involved. Appropriate data security controls reduce the likelihood (and impact) of data breach incidents during various phases of the data lifecycle. The purpose of this standard is to set out the rules for securing the companies' data during transmission and storage. This document provides best practice recommendations on information security management for use by those responsible for initiating, implementing or maintaining information security management systems (ISMS).
Nowadays, with the digitalization of our society, the need for data protection became more important. The latest IT Security Standards involve the application of technology to broader social and institutional contexts, and thereby contributes to the servitization of companies, and affects how they compete and interact. This document contains security technology solutions to protect data classified as “Highly Sensitive”, “Sensitive”, “Private” or “Public” as per the Data Classification Standard and Data Handling Guidelines. Specifically:
- Cryptography – Encryption and hashing solutions for protecting sensitive data when in transit or storage, and
- Data Masking – Data masking is a technology for obscuring sensitive information in non-production environments. Through data masking [Company Name] protects the content of sensitive data in non-production environments to ensure that:
- Application developers, testers, privileged users and outsourcing vendors do not have unauthorized access to such information.
- The data maintains the referential integrity of the original production data.
Feel free to download this intuitive template that is available in several kinds of formats, or try any other of our basic or advanced templates, forms or documents. Don't reinvent the wheel every time you start something new...
Download this Security Incident Report template and save yourself time and efforts! Besides this document, make sure to have a look at the IT Security Roadmap for proper implementation and this fit-for-purpose IT Security Kit here with over 40 useful templates. The document(s) are easy to modify and can be downloaded directly after purchase.
DISCLAIMER
Nothing on this site shall be considered legal advice and no attorney-client relationship is established.
发表评论。 如果您有任何问题或意见,请随时在下面发布
相关文件
Sponsored Link