Security Threat Assessment
Speichern, ausfüllen, drucken, fertig!
How to create a Security Threat Assessment? Download this Security Threat Assessment template now!
Verfügbare Gratis-Dateiformate:
.pdf- Dieses Dokument wurde von einem Professional zertifiziert
- 100% anpassbar
Business Unternehmen threat Drohung Compliance Regelkonformität IT information technology Informationstechnologie network Netzwerk Security Sicherheit Assessment Bewertung Trend Micro Mikro IT SOP GDPR DSGVO Threat Assessment Bedrohungsanalyse Iso GDPR template DSGVO Vorlage ccpa iso27001 isms ccpa template CCPA Vorlage nist standard iso it standard ISO IT Norm iso27001:2013 information security standards pdf Standards für Informationssicherheit PDF security standards definition Definition von Sicherheitsstandards network security standards Standards für die Netzwerksicherheit cyber security standards uk Cybersicherheitsstandards in Großbritannien cybersecurity Cybersicherheit cyber security compliance standards Beachtungsstandards für Cybersicherheit nist security standards information security standards Standards für die Informationssicherheit it security management IT Sicherheitsmanagement information security best practices Bewährte Vorgehensweisen für die Informationssicherheit information security policy standards Standards für Informationssicherheitsrichtlinien it security IT Sicherheit security techniques Sicherheitstechniken information security management systems Informationssicherheits Managementsysteme cybersecurity standards Standards für Cybersicherheit IT compliance IT Regelkonformität it standard operating procedure IT Standardarbeitsanweisung it security compliance Einhaltung der IT Sicherheit how long does it take to implement iso27001 Wie lange dauert die Implementierung von ISO27001? iso27001 questions iso27001 Fragen iso 27001 controls list iso 27002 checklist ISO 27001 Kontrollliste ISO 27002 Checkliste
Are you looking for a professional Security Threat Assessment? If you've been feeling stuck or lack motivation, download this template now!
This Security Threat Assessment can help you out. This Security Threat Assessment covers the most important topics and detects threats, such as:
• Worms
• Bots
• Trojans
• Crimeware
• Spyware/adware
• Network exploits
• Sensitive data loss
• Web-based threats (web exploits,
cross-site scripting)
• Email-based threats (phishing,
spear-phishing)
• Disruptive applications
A comprehensive security assessment report that details:
• Business Risk Meters: risks associated with detected threats
• Affected Assets: groups and endpoints affected by threats
• Threat Statistics: malware types found in the network
• Infection Sources: where the malware is coming from
• Disruptive Applications: which applications are causing the most problems
• Trends: trends of threats/events within your company
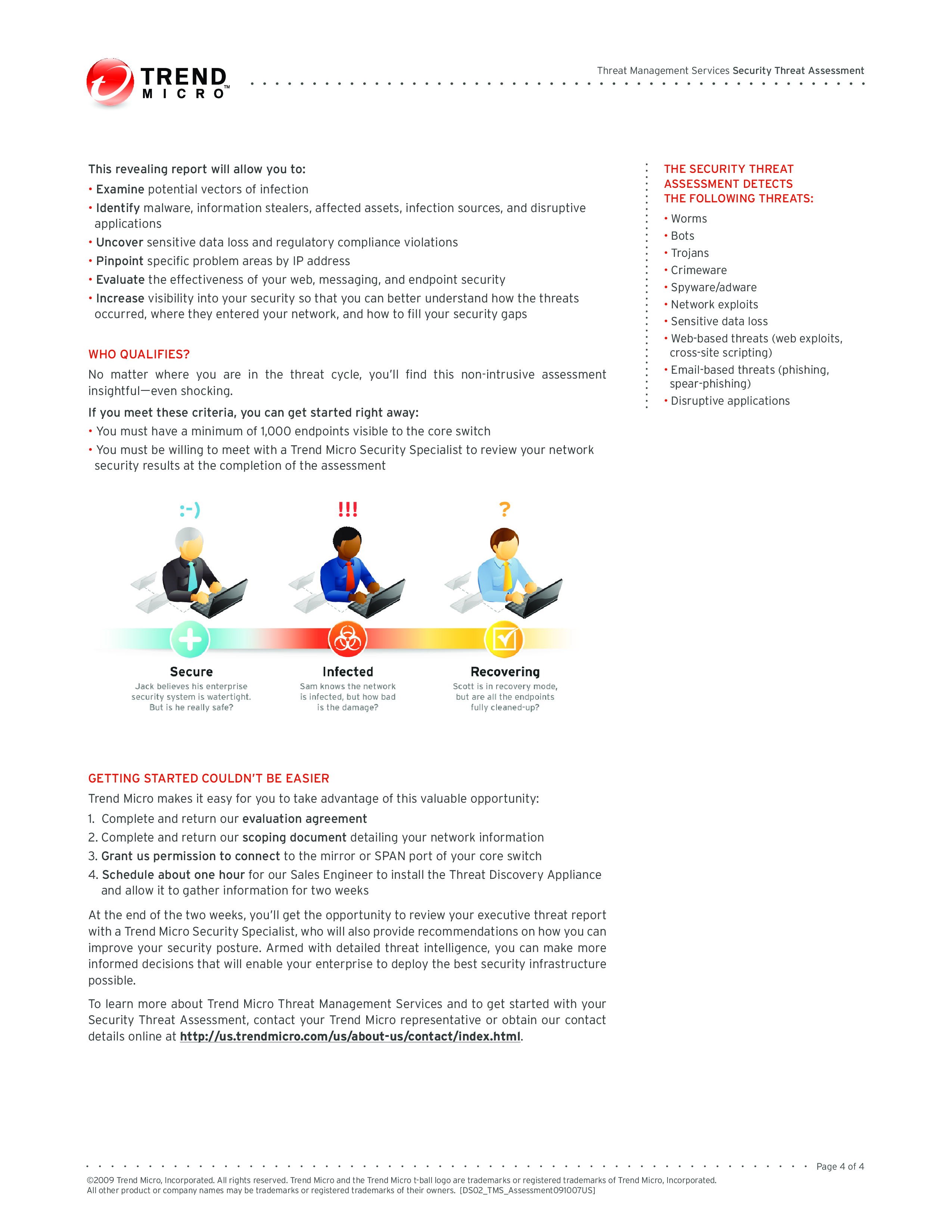
This revealing report will allow you to:
• Examine potential vectors of infection
• Identify malware, information stealers, affected assets, infection sources, and disruptive applications • Uncover sensitive data loss and regulatory compliance violations
• Pinpoint specific problem areas by IP address
• Evaluate the effectiveness of your web, messaging, and endpoint security
• Increase visibility into your security so that you can better understand how the threats occurred, where they entered your network, and how to fill your security gaps WHO QUALIFIES No matter where you are in the threat cycle, you’ll find this non-intrusive assessment insightful—even shocking.
Feel free to download this intuitive template that is available in several kinds of formats, or try any other of our basic or advanced templates, forms or documents. Don't reinvent the wheel every time you start something new...
Download this Security Threat Assessment template and save yourself time and effort! You will see completing your task has never been simpler! Besides this document, make sure to have a look at the IT Security Roadmap for proper implementation and this fit-for-purpose IT Security Kit here with over 40 useful templates. The document(s) are easy to modify and can be downloaded directly after purchase.
HAFTUNGSAUSSCHLUSS
Nichts auf dieser Website gilt als Rechtsberatung und kein Mandatsverhältnis wird hergestellt.
Wenn Sie Fragen oder Anmerkungen haben, können Sie sie gerne unten veröffentlichen.