Information Technology It Resume
Save, fill-In The Blanks, Print, Done!
Download Information Technology It Resume
Microsoft Word (.docx)Or select the format you want and we convert it for you for free:
- This Document Has Been Certified by a Professional
- 100% customizable
- This is a digital download (25.47 kB)
- Language: English
- We recommend downloading this file onto your computer.
How to grab your futures IT companies’ attention when you are applying for a job? How to draft a CSE Information Technology Resume that will impress your future employer(s)!
Our resume templates have ways to grab your employer’ attention. Every other essential piece of your document is covered. After downloading and filling in the blanks, you can customize every detail and appearance of your resume and finish in minutes.
When they are searching for a position in IT, consider they are often looking for someone with skills like:
- Computer Hardware Knowledge.
- Computer Software Knowledge.
- Internet Applications.
- Networks.
- Operating Systems.
- Troubleshooting.
- Internet Security.
- Data Privacy.
- Can do-will do mentality;
- Ability to communicate;
- Ability to multi-task;
- Hard work ethics;
- Creativity;
- Problem-solving ability.
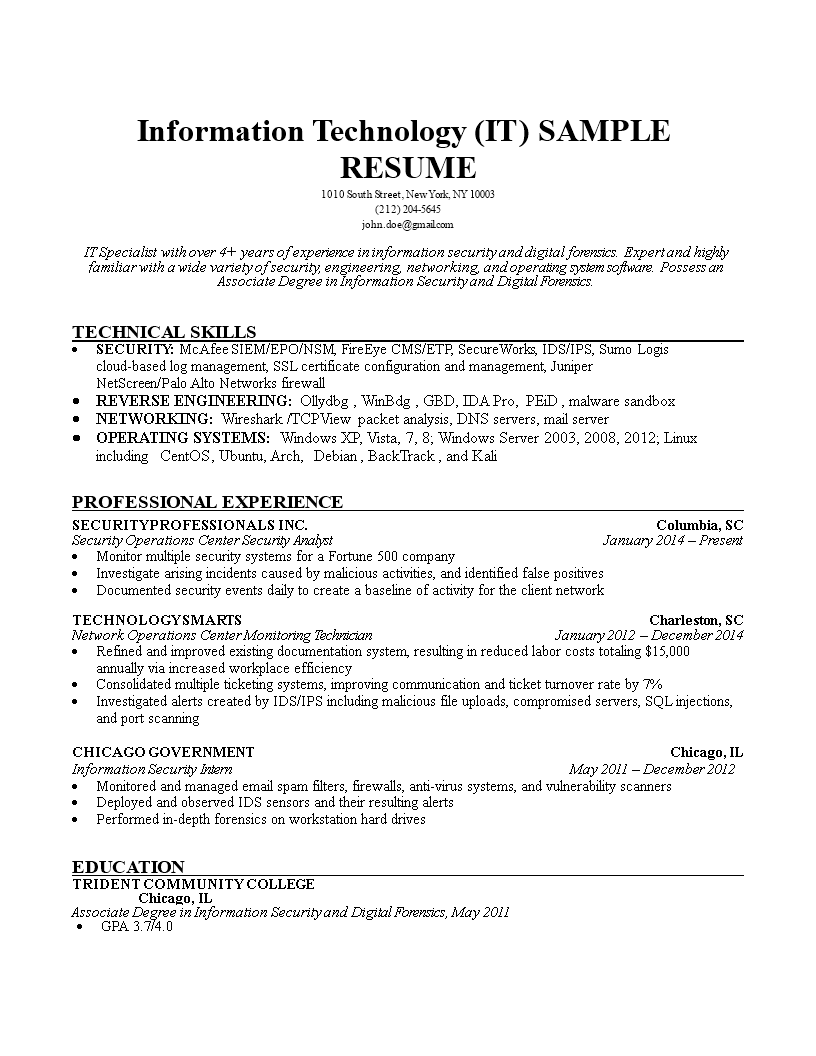
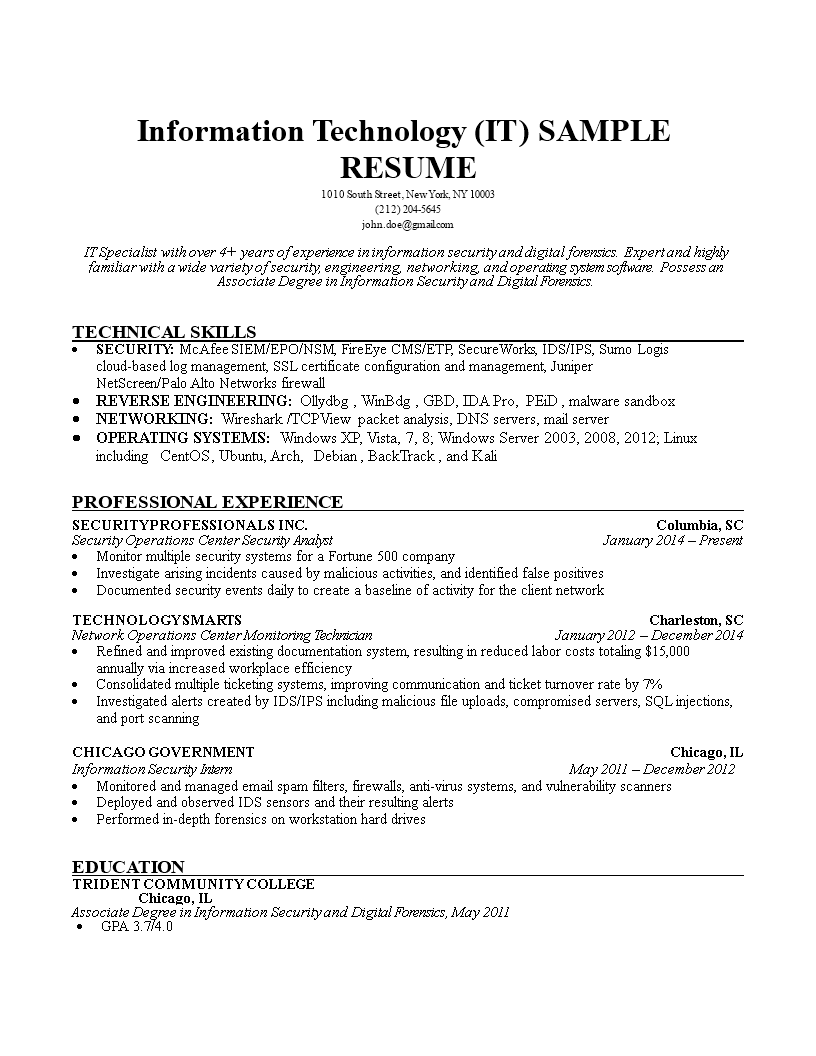
Information Technology Resume sample content:
Security Operations Center Security Analyst
Present Monitor multiple security systems for a Fortune 500 company
Investigate arising incidents caused by malicious activities, and identified false positives Documented security events daily to create a baseline of activity for the client network
TECHNOLOGY SMARTS Network Operations Center Monitoring Technician
Refined and improved existing documentation system, resulting in reduced labor costs totaling
15,000 annually via increased workplace efficiency
Consolidated multiple ticketing systems, improving communication and ticket turnover rate by Investigated alerts created by IDS/IPS including malicious file uploads, compromised servers,
SQL injections, and port scanning
GOVERNMENT Information Security Intern Monitored and managed email spam filters, firewalls, anti-virus systems, and vulnerability scanners
Deployed and observed IDS sensors and their resulting alerts Performed in-depth forensics on workstation hard drives
EDUCATION COLLEGE Associate Degree in Information Security and Digital Forensics
There are a few basic requirements for a resume. Every resume should contain the following:
- Brief, preferably one page in length
- Clean, error-free, and easy to read
- Structured and written to highlight your strengths
- Immediately clear about your name and the position you are seeking
Print out your Information Technology Resume and start modifying the file today...
DISCLAIMER
Nothing on this site shall be considered legal advice and no attorney-client relationship is established.
Leave a Reply. If you have any questions or remarks, feel free to post them below.
Related templates
Latest templates
Latest topics
- GDPR Compliance Templates
What You Need To Be DPR compliant? Are you looking for useful GDPR document templates to make you compliant? All these compliance documents will be available to download instantly... - Letter Format
How to format a letter? Here is a brief overview of common letter formats and templates in USA and UK and get inspirited immediately! - Excel Templates
Where to find usefl Excel templates? How do I create a template in Excel? Check these editable and printable Excel Templates and download them directly! - IT Security Standards Kit
What are IT Security Standards? Check out our collection of this newly updated IT Security Kit Standard templates, including policies, controls, processes, checklists, procedures and other documents. - Drop Shipping Agreement
How to start drop shipping? Do you need a Drop shipping Agreement? Check out our Dropshipping Agreement templates now!
cheese