Security Risk Management Plan
Save, fill-In The Blanks, Print, Done!
Download Security Risk Management Plan
Adobe Acrobat (.pdf)- This Document Has Been Certified by a Professional
- 100% customizable
- This is a digital download (221.42 kB)
- Language: English
- We recommend downloading this file onto your computer.
How to write a professional Security Risk Management Plan? Download this Security Risk Management Plan if you are working on IEC, NIST, ISO27001:2013 or other IT and Cyber Security Standards and control objectives.
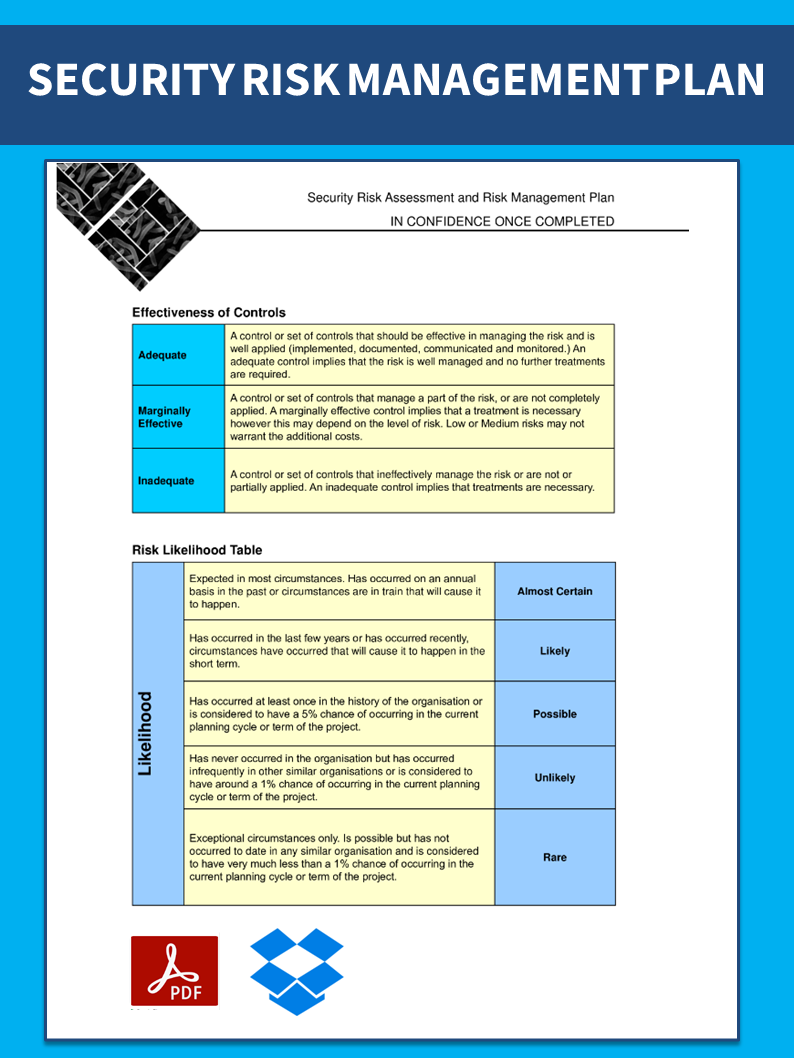
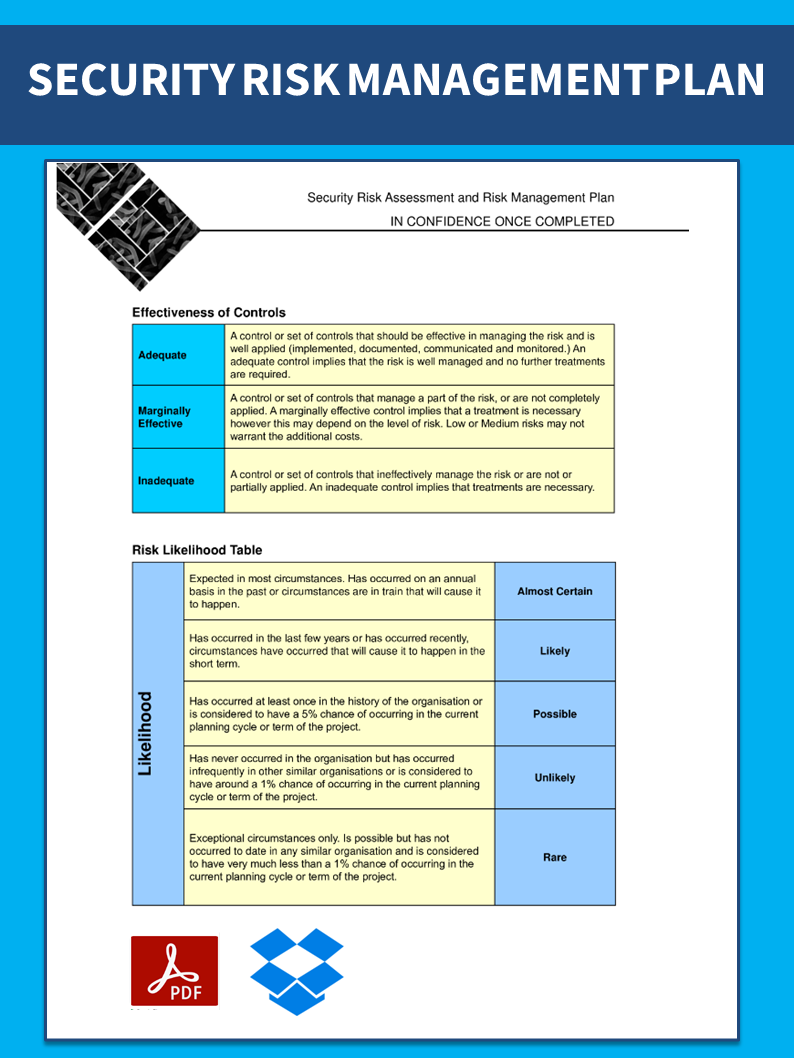
Security Risk Assessment and Risk Management Plan, Agents Regulatory Scheme Security Risk Template Government Department of Health and Ageing
- Security Risk Assessment and Risk Management Plan
- Approvals Prepared By:
- Section revised Government Department
- Security Risk Assessment and Risk Management Plan
- Introduction Security risk assessments provide an approach to support the identification, assessment, and management of security risks relating to the physical environment, personnel, sensitive information and incident management.
- Intense media interest over long term, serious public outcry, loss of credibility Deaths or multiple life-threatening Injuries Minor injury, medical treatment required Health and Safety Life-threatening injury or multiple serious injuries causing hospitalization, potential for permanent disability Ailments not requiring medical treatment or first aid only, no lost time or occupational illness Medium-term backlog or suspensions of work Indefinite backlog or suspension of work, significant additional resources required No material disruptions Critical Services disruptions Prolonged backlog or suspensions of work, additional resources required Short term backlog or suspensions of work Little or no impact, no financial loss Non achievement of objective, performance failures, financial loss of 30 to net revenue or assets Significant project delays, performance significantly under target, financial loss of 20 to net revenue or assets Material project delays, underachievement of target performances, financial loss
Feel free to download this intuitive template that is available in several kinds of formats, or try any other of our basic or advanced templates, forms or documents. Don't reinvent the wheel every time you start something new.
Appropriate data security controls reduce the likelihood (and impact) of data breach incidents during various phases of the data lifecycle. The purpose of this standard is to set out the rules for securing the companies' data during transmission and storage. This document provides best practice recommendations on information security management for use by those responsible for initiating, implementing or maintaining information security management systems (ISMS).
Nowadays, with the digitalization of our society, the need for data protection became more important. The latest IT Security Standards involve the application of technology to broader social and institutional contexts, and thereby contributes to the servitization of companies, and affects how they compete and interact. This document contains security technology solutions to protect data classified as “Highly Sensitive”, “Sensitive”, “Private” or “Public” as per the Data Classification Standard and Data Handling Guidelines. Specifically:
- Cryptography – Encryption and hashing solutions for protecting sensitive data when in transit or storage, and
- Data Masking – Data masking is a technology for obscuring sensitive information in non-production environments. Through data masking [Company Name] protects the content of sensitive data in non-production environments to ensure that:
- Application developers, testers, privileged users and outsourcing vendors do not have unauthorized access to such information.
- The data maintains the referential integrity of the original production data.
Download this Security Risk Management Plan now. Besides this document, make sure to have a look at the IT Security Roadmap for proper implementation and this fit-for-purpose IT Security Kit here with over 40 useful templates. The document(s) are easy to modify and can be downloaded directly after purchase.
Download this Security Risk Management Plan template and save yourself time and effort! You will see completing your task has never been easier.
DISCLAIMER
Nothing on this site shall be considered legal advice and no attorney-client relationship is established.
Leave a Reply. If you have any questions or remarks, feel free to post them below.
IT Security Standards Kit
What are IT Security Standards? Check out our collection of this newly updated IT Security Kit Standard templates, including policies, controls, processes, checklists, procedures and other documents.
Read moreRelated templates
Latest templates
Latest topics
- Business Credit Application Forms
How to create a Business Credit Application Form? Check out our Credit Application Form templates here. - GDPR Compliance Templates
What You Need To Be DPR compliant? Are you looking for useful GDPR document templates to make you compliant? All these compliance documents will be available to download instantly... - Letter Format
How to format a letter? Here is a brief overview of common letter formats and templates in USA and UK and get inspirited immediately! - Excel Templates
Where to find usefl Excel templates? How do I create a template in Excel? Check these editable and printable Excel Templates and download them directly! - IT Security Standards Kit
What are IT Security Standards? Check out our collection of this newly updated IT Security Kit Standard templates, including policies, controls, processes, checklists, procedures and other documents.
cheese