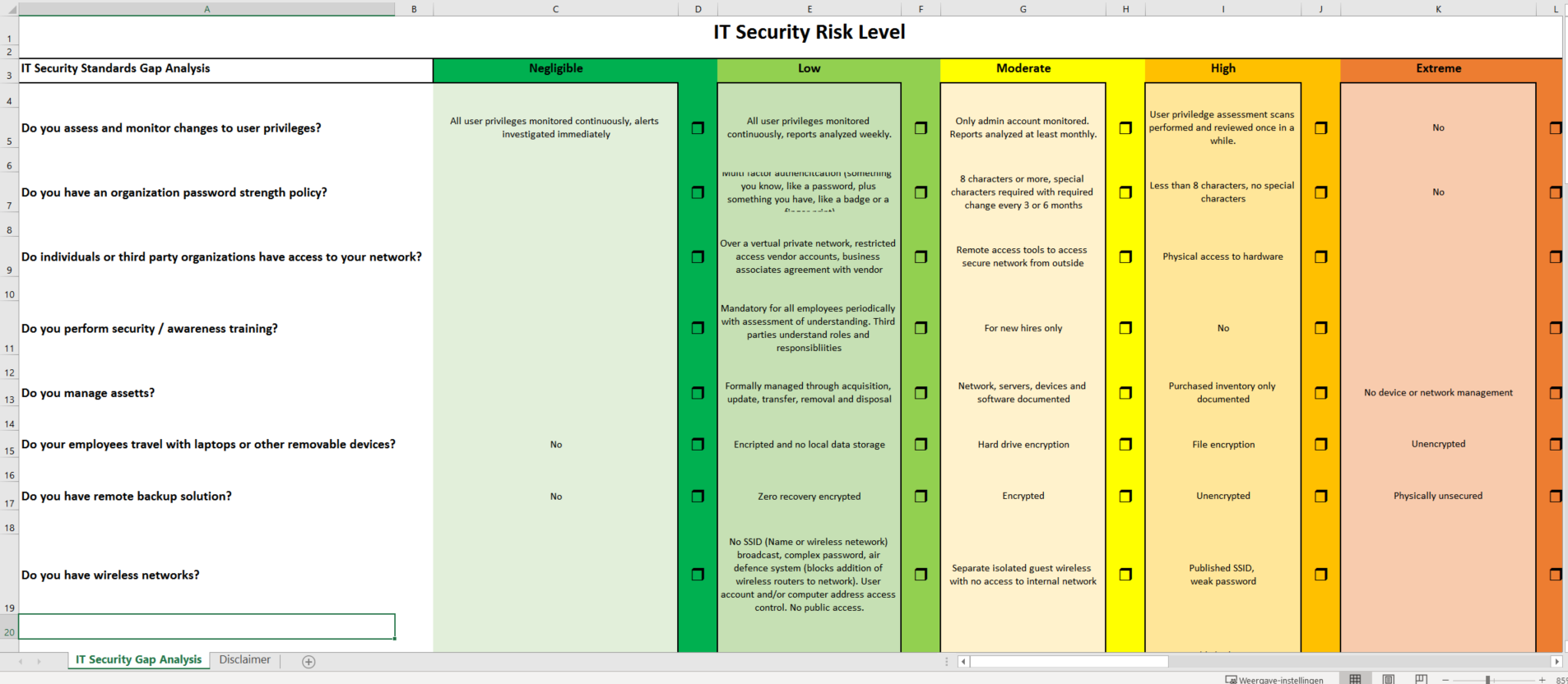
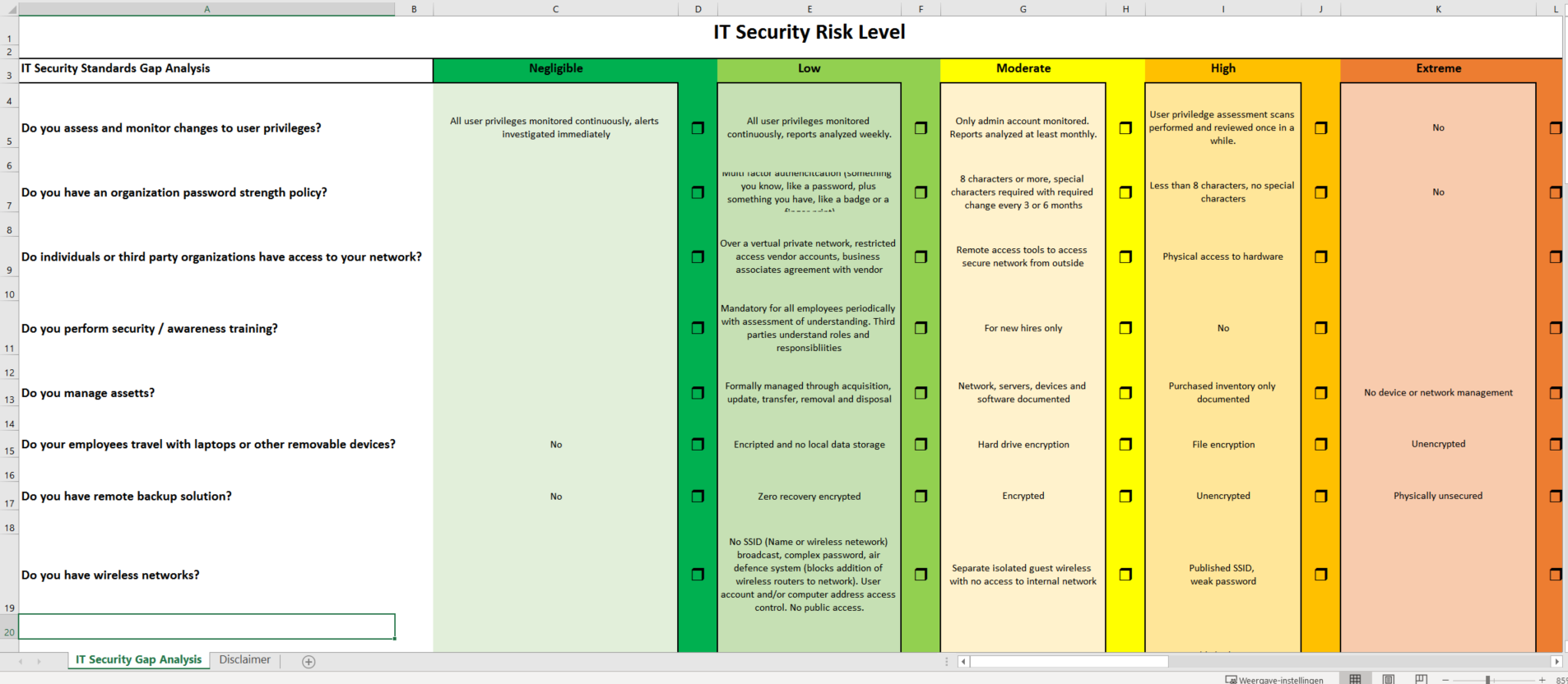
Internal IT Security Gap Analysis
Save, fill-In The Blanks, Print, Done!
Download Internal IT Security Gap Analysis

Available premium file formats:
Microsoft Spreadsheet (.xlsx)- This Document Has Been Certified by a Professional
- 100% customizable
- This is a digital download (30.95 kB)
- Language: English
- You will receive a link to download the file as soon as your payment goes through.
- We recommend downloading this file onto your computer.
- Do you assess and monitor changes to user privileges?
- Do you have an organization password strength policy?
- Do individuals or third-party organizations have access to your network?
- Do you perform security/awareness training?
- Do you manage assets?
- Do your employees travel with laptops or other removable devices?
- Do you have a remote backup solution?
- Do you have wireless networks?
- Cryptography – Encryption and hashing solutions for protecting sensitive data when in transit or storage, and
- Data Masking – Data masking is a technology for obscuring sensitive information in non-production environments. Through data masking [Company Name] protects the content of sensitive data in non-production environments to ensure that:
- Application developers, testers, privileged users and outsourcing vendors do not have unauthorized access to such information.
- The data maintains the referential integrity of the original production data.
DISCLAIMER
Nothing on this site shall be considered legal advice and no attorney-client relationship is established.
Leave a Reply. If you have any questions or remarks, feel free to post them below.
IT Security Standards Kit
What are IT Security Standards? Check out our collection of this newly updated IT Security Kit Standard templates, including policies, controls, processes, checklists, procedures and other documents.
Read moreRelated templates
Latest templates
Latest topics
- GDPR Compliance Templates
What You Need To Be DPR compliant? Are you looking for useful GDPR document templates to make you compliant? All these compliance documents will be available to download instantly... - Letter Format
How to format a letter? Here is a brief overview of common letter formats and templates in USA and UK and get inspirited immediately! - Excel Templates
Where to find usefl Excel templates? How do I create a template in Excel? Check these editable and printable Excel Templates and download them directly! - IT Security Standards Kit
What are IT Security Standards? Check out our collection of this newly updated IT Security Kit Standard templates, including policies, controls, processes, checklists, procedures and other documents. - Drop Shipping Agreement
How to start drop shipping? Do you need a Drop shipping Agreement? Check out our Dropshipping Agreement templates now!
cheese